Hosting
Xneelo (Hetzner)
By default, clients are hosted at Hetzner's main data centre in Johannesburg with a standby micro instance at Microsoft Azure. Hetzner's data centres are all equipped with CCTV cameras and access is granted to Hetzner employees via biometric access. We try our absolute best to secure your data and prevent unauthorised access while keeping your data accessible whenever it is needed.
Microsoft Azure
Clients can opt to host in Microsoft Azure's data centre in the South Africa North region by paying an extra monthly fee. Azure has more regions than any other cloud provider and they provide complaint and resilient solutions. Backups are handled by Azure and they ensure that all servers remain accessible.
On Premises
Clients can opt to host TaskFlow on premises if there is a very good reason for wanting to do so. In this case it is the client's responsibility to provide us with a server and to ensure that access is restricted to the server. Clients also have the responsibility to perform daily backups and maintenance.
Availability SLA
Our server infrastructure will improve over time. At the time of writing we are able to provide a 99.9% uptime to our clients. This excludes the on premise clients since we cannot control all the variables, such as power supply to the server and network uptime.
| Availability % | Downtime per year |
|---|---|
| 99 | 3.65 days |
| 99.9 | 8.76 hours |
| 99.99 | 52.56 minutes |
| 99.999 | 5.26 minutes |
| 99.9999 | 31.5 seconds |
Backups / Disaster Recovery
We keep 7 days full backups for each TaskFlow database. Backups are replicated via a secure channel between regions as well as to a physical location. Backups are made at 02:00 every day. Backups are not sent across the boarder - i.e. the data remains in South Africa.
Hardware failure
- Hard drives are set up in either RAID 1 or RAID 5 configuration ensuring no data loss due to the failure of a single drive
- Servers have multiple network interfaces that are set up in a Linux Bond ensuring that traffic can be routed in case an interface becomes unavailable
- Servers have a dual hot-swappable power supply, ensuring uptime even if one power supply fails
Disaster recovery
- RPO (Recovery Point Objective): Clients will never lose more than 24 hours of data. This will only happen when we are unable to restore a slave server and have to restore your TaskFlow instance from the previous days' backup.
- RTO (Recover Time Objective): Clients will be offline for a maximum of 4 hours in case an entire data centre becomes unavailable.
Servers are constantly monitored and TaskFlow system administrators are notified whenever crucial events occur.
Database security
Your database is only accessible via your TaskFlow URL (e.g. demo.taskflow.co.za). Although all clients' databases run on one cluster there is no data sharing between clients' databases what so ever. Your database is replicated over a secure connection using key pair authentication.
Direct database access (read-only) can be provided to clients who wish to mine their data with BI tools. An email can be sent to support@taskflow.co.za to request access. We will follow the necessary steps to ensure that the person requesting access is authorised to do so.
Password security
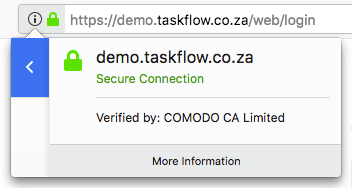
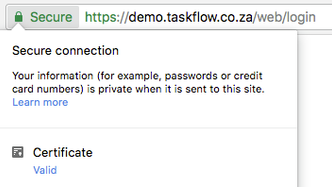
Login details are hashed using industry standard hashing techniques. Not even TaskFlow staff has access to your passwords. In the event that a client loses their password, the only option is to send password reset instructions. When logging into TaskFlow, your data is always transmitted via HTTPS. You can verify this from within the browser by making sure that a "lock" icon is present.
Employee access
TaskFlow employees have access to the administrator account on your TaskFlow instance. We may log on from time to time in order to assist with support requests. We use our discretion to only access data that relates to the support request and we have policies in place to ensure that TaskFlow employees do not copy data without authorisation from the client.
System security
Only a select few TaskFlow engineers have access to the server clusters. The only means of logging in is using secure key pair authentication via SSH. We only allow TaskFlow engineers access to the server clusters from our office's location (i.e. no access is granted to any IP address other than our static IP at our office).
We use a hardened Linux distribution as our operating system and have configured our firewall to only allow access on certain ports. Our servers are also resilient against DDoS attacks. We make every best effort to adhere to best practice / standards when securing our network, infrastructure and data.
Software security
TaskFlow as a framework is designed in such a way that it prevents all of the most common types of attacks:
- SQL injections are impossible since the ORM ensures that no piece of code can manually execute SQL statements
- The framework's templating engine ensures that XSS attacks are impossible by using various techniques such as escaping all data that is rendered
- RPC calls do not have access to private methods in the framework
- The login page is rendered with a CSRF token which makes Cross Site Request Forgery impossible
- All code evaluations are done in a sandboxed environment making RFI attacks impossible
Software updates
All code changes made to the TaskFlow framework is evaluated and reviewed by TaskFlow engineers through a peer review process. In addition, our automated testing platform performs unit tests and code auditing and provides our engineers with reports that are used to determine if changes introduce any bugs or regressions.
Changes are carefully written up and compiled in a new version release document which is distributed to clients prior to deploying new versions. Opportunity for feedback is given and our engineers ensure that upgrades always result in a better product for the user.